Operational Security
Our application is exclusively developed and managed by our internal Engineering Team. External vendors are never granted access to any component of our code, databases, or application infrastructure.
Access to the database and server is limited to Engineering Team members and is based strictly on a need-to-know principle.
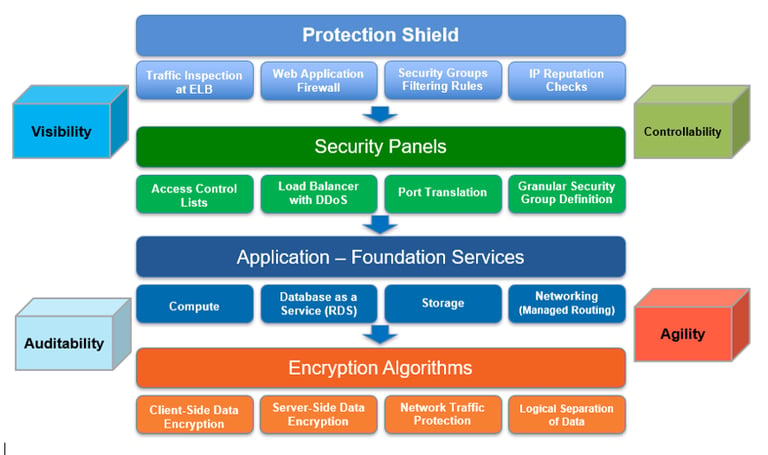
Top-tier security infrastructure and privacy safeguards.
At DIGITAL EVOLVE, ensuring security is our top priority. We adhere to SOC compliance and are dedicated to upholding the processes and controls that enhance the security and privacy of all our customers. DIGITAL EVOLVE employs best-practice security measures throughout the development of our platform, with every new feature designed with security considerations in mind, adhering to the Service Organization Control (SOC) standards. The SOC 2 report signifies an audit of our controls concerning the criteria of Security, Availability, and Confidentiality. We consistently reassess and test our security protocols to ensure we meet industry standards and best practices.
Security
DDoS Mitigation
DIGITAL EVOLVE analyzes incoming traffic at various points using web application firewall (WAF) entry points to identify and whitelist legitimate traffic while filtering out malicious and low-reputation traffic patterns, thereby protecting the platform.
Single Sign-On (SSO) Authentication Configuration
To access DIGITAL EVOLVE, authentication can be configured through a supported SSO provider, including Office365, Google G-suite, Okta, OneLogin, or SAML-based systems.
Clients may also implement additional security policies for SSO access, such as requiring Multi-Factor Authentication (MFA).
For added security, access to DIGITAL EVOLVE is limited to a predetermined range of IP addresses.
Encryption
Information exchanged between your browser and our application is secured with 256-bit SSL certificates that meet banking standards.
Sensitive information held in our database is protected through 256-bit AES encryption, using a distinct master key for each customer.
Account passwords are safeguarded with one-way encryption, ensuring they cannot be retrieved in plain text (not even by us).
Each customer's data is isolated within a unique and secure database environment
Application and Systems Security
We adhere to industry best practices to protect against man-in-the-middle attacks, injection attacks, and cross-site request forgery.
Access to our production servers is limited to specifically authorized devices, such as those used by our Engineering Team, in accordance with stringent access and usage policies.
We enforce rigorous firewall and authentication protocols throughout the product.
Data Center
Our infrastructure is hosted on Microsoft Azure data centers. You can find more details about their security practices at: http://
Audit Logs and Monitoring
DIGITAL EVOLVE maintains detailed audit logs covering all customer and user transactions, systems access, and network operations.
Passwords, social security numbers, and other sensitive information are automatically stripped out from log files and audit records. This sensitive information is not stored in the forms collected.
DIGITAL EVOLVE monitors the infrastructure 24×7 using a combination of third-party monitoring services.
Data Protection
We implement a robust backup system that automatically and continuously replicates production data to multiple secure locations, ensuring data integrity and minimizing downtime.
Our infrastructure is designed for high availability, with hot backup records maintained to guarantee seamless continuity in the event of an outage.
Our backup data is safeguarded with the same stringent security protocols as our primary production environment.

DIGITAL EVOLVE requires all its personnel to follow an Information Security Policy that ensures that any devices used for company purposes follow security best practices.
DIGITAL EVOLVE only grants its personnel access to resources on a “need-to-know” basis.
DIGITAL EVOLVE also requires its personnel to use a secure communication channel to exchange any information internally..